
Design plan and deploy Cyber-Security Solutions | Juniper Networks
Project description
Daniel Cortez Security Assessment
Implement secure encryption technologies
Design and implement a security perimeter for ICT networks
Install and maintain valid authentication processes
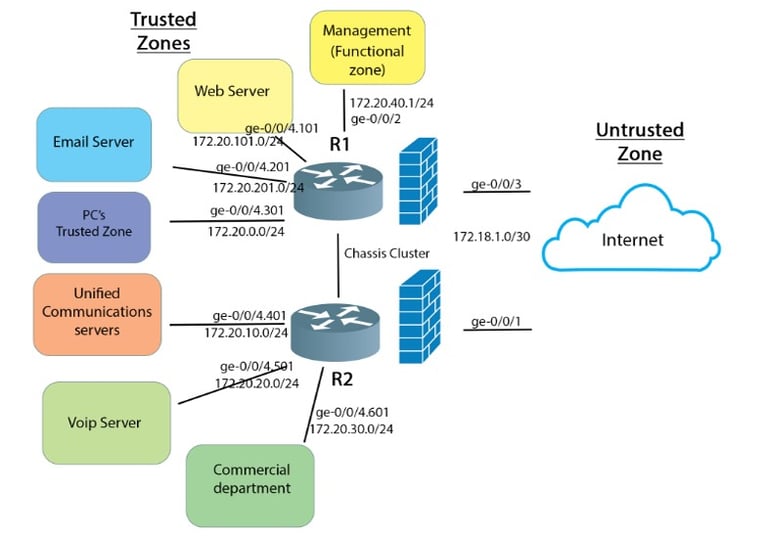
Redesign the network security infrastructure for A company to meet the organization’s business requirements, and write a detailed proposal which I submitted to Spyon Technologies for consideration.
The final design proposal to the company included the following:
a detailed list of business requirements that must be met by the network security design
a complete and detailed discussion of the network security design proposal. This must include complete logical diagrams of the redesigned network and a discussion of the techniques and technologies used, e.g. Clustering, zones, policies, authentication, encryption, and VPN’s
details of how the network security design will meet all the business requirements
Prepare implementation plans
Document the network design and present the documentation to the appropriate person for approval
Present the design in a clear and logical fashion
Provide advice to the client on reasons for the design choice.
Scenario
My work in the cyber security division as a network engineer. My role is to assist with the planning and implementation of security measures and general network infrastructure.
IT Services The company uses the following server technologies:
1. Web servers for the company intranet and Web applications. This is accessed by remote workers.
2. Mail servers – Used by internal and external staff
3. Unified Communications servers
Tasks
1. The security perimeter must prevent all unauthorized access to company data.
2. All WAN links must be encrypted and secured.
3. All electronic communication within the company and with third parties must be encrypted and digitally signed.
4. Measures must be put in place to protect against DOS, DDOS, viruses, and all other cyber security threats.
5. The solution must be fault tolerant by eliminating single points of failure
Task 2
In order to calculate the risk level for each risk that is to be examined, it is necessary to calculate the impact of the threat occurring and the likelihood (or probability) of the threat occurring.
Make a list of possible cyber security threats. Allocate each threat an impact level, likelihood, and risk level.
Task 3
Using the list of threats, create a table that lists the defenses for each threat
Task 4
Design the firewall configuration
The design should include the following:
a. The name of each security zone I create
b. The inter-zone policy objectives
c.Traffic allowed into the zone
d. Traffic allowed between the zones
e. Other security measures to be implemented in the policy
f. Method of securing traffic from site to site
g. Method of securing traffic to and from the public internet
Task 5
Write the Juniper SRX configuration required to implement all the functionality described.. Provide the IP addressing scheme as a separate table.
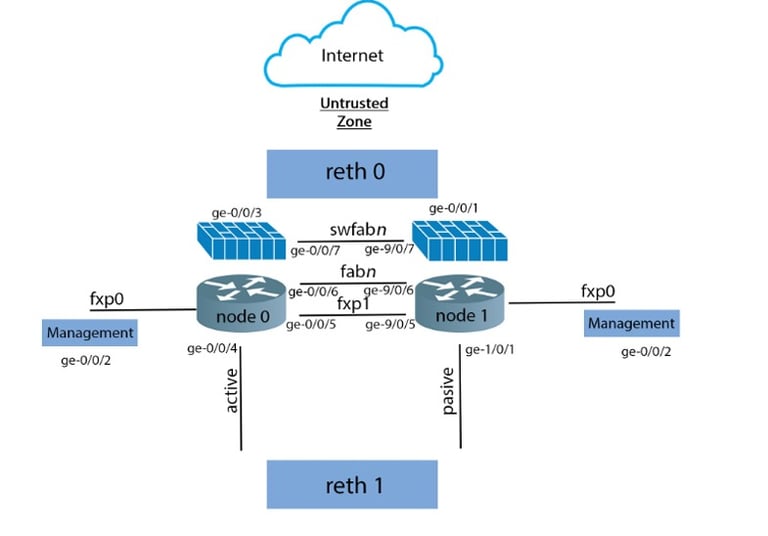
Task 6
Design failover redundancy for the firewall so that a stateful failover of processes and services will occur in the event of system or hardware failure. Provide a diagram of the design and a description of how failover will be achieved in the event of a failure.
Task 7
Provide a typical failover redundancy configuration for a Juniper SRX firewall
Task 8
Provide a typical site to site VPN configuration for a Juniper SRX firewall.
Task 9
Is the network traffic traversing the IPSEC VPN encrypted using symmetric or asymmetric encryption? Compare 3 algorithms that could be used to encrypt the IPSEC VPN traffic. List the tests I performed to verify that the security measures and VPN are functioning as expected.
Questions?
Whether you’re curious about features, or vital information, we’re here to answer any questions.


